Pi-hole's Default Block Lists
List Formats
It's very important that whatever lists you decide to add to Pi-hole are in HOSTS format. Pi-hole's knows how to parse these lists. As you'll see below, things like Adblock Plus' EasyLists can't be automatically imported into Pi-hole.
If you are interested in adding additional domains to block, check out WaLLy3K's blocklist compilation.
Easiest way to add additional lists
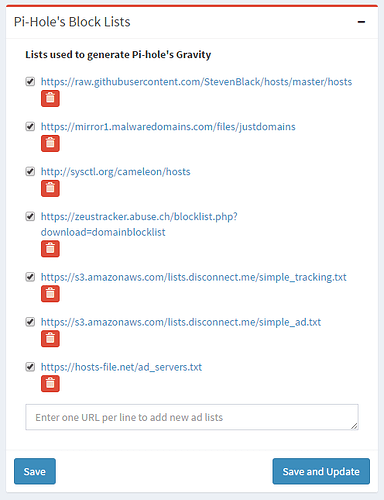
UPDATE: As of version 3.0, adlist management can now be done via the web UI, you no longer need to touch the command line for this!
By default, when pihole -g pulls in lists of domains to block, we combine several lists, which are defined in /etc/pihole/adlists.list:
# The below list amalgamates several lists we used previously.
# See `https://github.com/StevenBlack/hosts` for details
##StevenBlack's list
https://raw.githubusercontent.com/StevenBlack/hosts/master/hosts
##MalwareDomains
https://mirror1.malwaredomains.com/files/justdomains
##Cameleon
http://sysctl.org/cameleon/hosts
##Zeustracker
https://zeustracker.abuse.ch/blocklist.php?download=domainblocklist
##Disconnect.me Tracking
https://s3.amazonaws.com/lists.disconnect.me/simple_tracking.txt
##Disconnect.me Ads
https://s3.amazonaws.com/lists.disconnect.me/simple_ad.txt
##Hosts-file.net
https://hosts-file.net/ad_servers.txt
If you add any domains, then they can go anywhere in the file, so long as they are not commented out (prefixed with #)
Block More Than Advertisements
By using alternate lists, you have the ability to block tracking sites, malware domains, known spam servers, and more.
We've included many of these lists in adlists.default, but they are commented out. In order to use them, copy adlists.default to adlists.list and uncomment them.
These Lists Will Need Additional Parsing Logic
The lists below are not in standard hosts format. Since Pi-hole blocks ads at the DNS level, just the domain name needs to be extracted from the lists. To do this, you will likely need to use sed and awk to parse down to get just the domain names.
http://jansal.googlecode.com/svn/trunk/adblock/hostshttp://www.sa-blacklist.stearns.org/sa-blacklist/sa-blacklist.currenthttps://easylist-downloads.adblockplus.org/malwaredomains_full.txthttps://easylist-downloads.adblockplus.org/easyprivacy.txthttps://easylist-downloads.adblockplus.org/easylist.txthttps://easylist-downloads.adblockplus.org/fanboy-annoyance.txthttp://www.fanboy.co.nz/adblock/opera/urlfilter.inihttp://www.fanboy.co.nz/adblock/fanboy-tracking.txt
How To Parse A List To Get Just The Domain
Imagine you found a list you want to use, but it is formatted with a bunch of extra characters:
||unlimited-hacks.net^
||pakcircles.com^
||cracksplay.com^
||fbgamecheatz.info^
||linkz.it^
You can use sed and/or awk (or other commands) to remove the extra characters to get just the domain name. It helps to be familiar with scripting, but if you wanted to parse down the list above, you could do something like this:
curl -s http://some.list | sed 's/^||//'
This would remove the two pipes at the beginning of the lines, so your list would then look like this:
unlimited-hacks.net^
pakcircles.com^
cracksplay.com^
fbgamecheatz.info^
linkz.it^
Then, you could use sed again, or even something like cut. Since the domains won't have a carat in the name, you can use it as a delimiter with the cut command to display only the domain name.
curl -s http://some.list | sed 's/^||//' | cut -d'^' -f-1
Which leaves you with just the domain names:
unlimited-hacks.net
pakcircles.com
cracksplay.com
fbgamecheatz.info
linkz.it
There is more than one way to parse the list down and there is no right way, however, some methods are faster. If you can combine most of your parsing into a single awk command, it can process a large list much faster. For each | that you use in the command, you are slowing down the processing as it is running in another subshell.