##![]() THIS TUTORIAL ONLY WORKS WITH DNSCRYPT VERSION 1.9.1 OR EARLIER
THIS TUTORIAL ONLY WORKS WITH DNSCRYPT VERSION 1.9.1 OR EARLIER ![]()
See: dnscrypt-proxy v1.9.3 doesn't work with dnscrypt-loader · Issue #11 · GortCodex/DNSCrypt-Loader · GitHub
If you wish to use DNScrypt 1.9.3 and later, use this tutorial: https://github.com/pi-hole/pi-hole/wiki/DNSCrypt
This tutorial is based on Debian 8, results may vary. This tutorial will help you easily set up DNScrypt. Bits and pieces of this tutorial will be pulled from https://github.com/pi-hole/pi-hole/wiki/DNSCrypt.
##Install packages (from wiki):
sudo apt-get update
sudo apt-get -y install build-essential tcpdump dnsutils libsodium-dev
sudo apt-get -y install locate bash-completion libsystemd-dev pkg-config
##Building DNScrypt (from wiki):
mkdir -p dnsproxy
cd dnsproxy
wget https://download.dnscrypt.org/dnscrypt-proxy/dnscrypt-proxy-1.9.1.tar.gz
tar -xf dnscrypt-proxy-1.9.1.tar.gz
ls
cd dnscrypt-proxy-1.9.1
sudo ldconfig
./configure
make
sudo make install
##Installing DNScrypt-Loader
Assuming we're still working in ~/dnsproxy/
Necessary package if not already installed:
apt-get install gawk
Downloading DNScrypt-Loader files (GitHub - GortCodex/DNSCrypt-Loader: A flexible and customizable bash script to manage DNSCrypt-proxy)
wget https://github.com/GortCodex/DNSCrypt-Loader/archive/v1.2.tar.gz
tar -xf v1.2.tar.gz
cd DNSCrypt-Loader-1.2
##Setting Up DNScrypt-Loader
sudo ./install-loader-debian
After you run the command you will see a prompt, press OK.
After that you will come to this screen:
Choose option 1 to Install DNSCrypt-loader
When you see this screen, choose YES to continue:
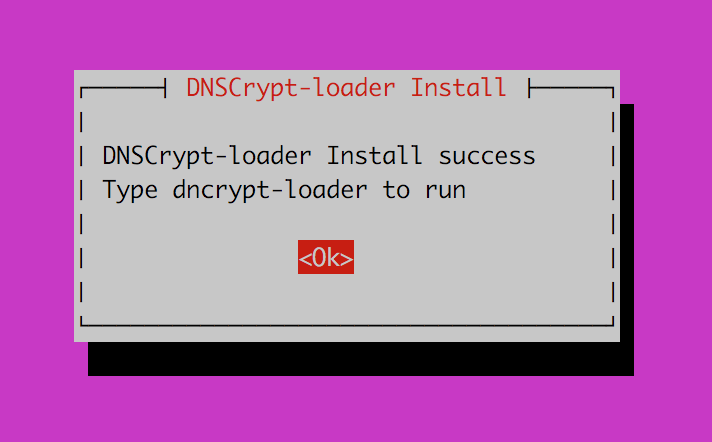
On successful installation you will see:
After you click on OK you will be redirected to the main page.
OPTIONAL STEP This time, choose option 2 to enable DNSCrypt to automatically start at boot.
When done, you can choose option 5 to quit or tab to CANCEL
##Configuring DNScrypt-Loader for use
nano /usr/local/sbin/dnscrypt-loader
Change these lines from:
cPrimaryIP="127.0.0.1"
cPrimaryPort="5553"
cSecondaryIP="127.0.0.1"
cSecondaryPort="5554"
to
cPrimaryIP="127.10.10.1"
cPrimaryPort="5553"
cSecondaryIP="127.10.10.2"
cSecondaryPort="5554"
or any ip / port you want... When done, EXIT and SAVE.
##Using DNScrypt-Loader
Launch DNScrypt-Loader using
sudo dnscrypt-loader
You should see a screen like such:
-
Your first step should be to choose option 7 to Update resolver.csv from official source
-
When you're done with that, choose option 1 to Set a Primary DNS resolver. Choose a resolver from the list. You can also set a secondary resolver.
-
Use this list to help you choose the best resolver. You should go for the ones that don't keep logs. (https://github.com/jedisct1/dnscrypt-proxy/blob/master/dnscrypt-resolvers.csv)
-
When you're done, you can choose option 10 to QUIT or tab to CANCEL
##Change DNSmasq config (from wiki):
sudo nano /etc/dnsmasq.d/02-dnscrypt.conf
add the following:
server=127.10.10.1#5553
server=127.10.10.2#5554
or whatever ip/port combination you chose to use.
From
sudo nano /etc/pihole/setupVars.conf
Comment out:
#piholeDNS1=...
#piholeDNS2=...
From
sudo nano /etc/dnsmasq.d/01-pihole.conf
Comment out
#server=...
Then
sudo service dnsmasq restart
##Testing your setup
Use http://dnsleaktest.com to ensure you've successfully set up DNScrypt-proxy.
##Upgrading and Uninstalling DNScrypt:
https://discourse.pi-hole.net/t/setting-up-and-using-dnscrypt-loader/606/5