Info
Linksys Velop is a mesh wifi system made up of nodes that work together to provide network coverage, parental controls and so on. It has various modes of operation, but a common one for home users is where it is added to an existing network and picks up its networking from an existing router via DHCP.
One of its functions is to find and identify devices on the network so they can be presented in the Velop app. Each node makes tens to hundreds of PTR requests every minute to the network's DNS server. Normally this traffic would not be visible because it would be handled by the router's DNS server.
Pi-hole can be configured in different ways but one common approach is to ammend the router's DHCP to stop using the router for DNS and switch to using Pi-hole for DNS. Another common approach is to disable the router's DHCP entirely and enable Pi-hole's DHCP to replace it. This way Pi-hole always presents itself as the DNS server.
Either way, with Pi-hole as the DNS server, Pi-hole users will now see all the Velop PTR traffic. These swamp the Query Log and graphs and make them difficult to use for other devices on the network.
Fix
One way to deal with this would be to make the Velop nodes revert to using the original router for DNS. However, on checking, it may be the case that the network settings cannot be edited and are fixed as DHCP.
If Pi-hole is the DHCP server there is a way to make it tell just the Velop nodes to use the original router for DNS, while everything else continues to use Pi-hole as normal. This was mentioned by @yubiuser and there is an external template for it by another user.
I've tested this with a friend who has these Velop mesh nodes and it has fixed the problem. They are no longer sending PTR requests to Pi-hole. They continue to find and show devices on the network, and features like parental control continue to work. All other devices continue to use Pi-hole as normal.
Steps
Identify nodes
Use Pi-hole's Dashboard graph to identify how many nodes are flooding it with PTR queries. Find these nodes in Tools > Network and make a note of their MAC addresses. You will probably find that the Velop parent node is not sending PTR requests, it is just the child nodes.
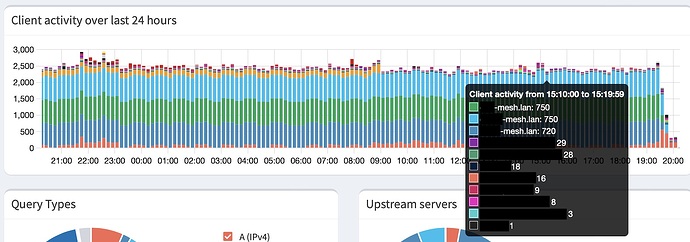
So if you have, eg, 4 Velop nodes, 1 is set as parent and the other 3 are child nodes, you would only need to configure those 3 nodes in the next section. This is my friend's graph and you can see the 3 child nodes dominating the graph.
Create bypass config
Log into the Pi-hole terminal and edit a new dnsmasq config file:
sudo nano /etc/dnsmasq.d/90-bypass.conf
Paste in the text
# Send Velop DNS to router rather than Pi-hole
# The config below is for 3 Velop nodes
# Copy and paste the Velop node sections to add more
# or delete unwanted sections for fewer
# Define router (replace xxx's with IP address of original router)
dhcp-option=tag:router,6,xxx.xxx.xxx.xxx
# Velop node 1 (replace XX's with node's MAC address
dhcp-host=XX:XX:XX:XX:XX:XX,set:router
# Velop node 2 (replace XX's with node's MAC address
dhcp-host=XX:XX:XX:XX:XX:XX,set:router
# Velop node 3 (replace XX's with node's MAC address
dhcp-host=XX:XX:XX:XX:XX:XX,set:router
Edit the text and replace the xxx's with the original router's IP address. Replace the XX's with the MAC addresses of the Velop nodes that are sending PTR requests, identified in the previous step. If you have more than 3 nodes doing this, copy and paste the Velop sections to add more. If you have fewer then delete the unwanted sections. Each section should have a valid MAC address.
Save the file and quit nano.
Activate new config
Reboot the Pi-hole. This is a simple way to make sure the changes have definitely taken and are working across reboots.
Finally, reboot all the Velop nodes. This forces them to reconfigure the mesh. When they come back up and do a DHCP request, the Pi-hole will answer and give them the address of the original router for DNS. Everything else on the network, including devices attached to the nodes, will continue to use Pi-hole for DNS.
Check results
Observe the graph and Query Log and you will see the nodes are no longer flooding them with queries, as these are now going to the router's DNS to deal with. You can see that at the end of the above graph. Here's an image of it hours later looking much better. Once the busy part of the graph has scrolled off the left side the graph scale will adjust back to normal.
Any other Velop functions used prior to the change, such as Parental Control, will continue to work after the change.
Revert if ever needed
Log into the Pi-hole terminal and delete the config file
sudo rm /etc/dnsmasq.d/90-bypass.conf
Reboot the Pi-hole and once it's back up reboot the Velop nodes. They will revert to using Pi-hole for DNS.