Hey,
i followed the official documentation for unbound as an recursive resolver and I want to use it.
Currently my pihole uses stubby for DoT.
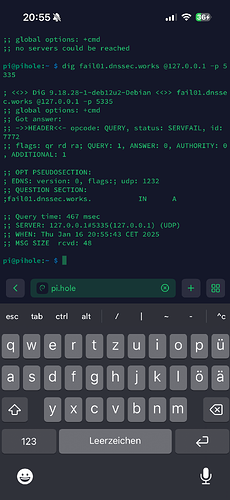
The first tests on console says there is an "communication error" on unbound. This error doesn't happen always but often.
I'm using Raspian as OS.
pi@pihole:dig pi-hole.net @127.0.0.1 -p 51234
;; communications error to 127.0.0.1#51234: timed out
;; communications error to 127.0.0.1#51234: timed out
;; communications error to 127.0.0.1#51234: timed out
; <<>> DiG 9.18.28-1~deb12u2-Debian <<>> pi-hole.net @127.0.0.1 -p 51234
;; global options: +cmd
;; no servers could be reached
Sometimes it works
pi@pihole:~ $ dig pi-hole.net @127.0.0.1 -p 51234
; <<>> DiG 9.18.28-1~deb12u2-Debian <<>> pi-hole.net @127.0.0.1 -p 51234
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 2958
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 1232
;; QUESTION SECTION:
;pi-hole.net. IN A
;; ANSWER SECTION:
pi-hole.net. 262 IN A 3.18.136.52
;; Query time: 0 msec
;; SERVER: 127.0.0.1#51234(127.0.0.1) (UDP)
;; WHEN: Fri Jan 10 14:43:29 CET 2025
;; MSG SIZE rcvd: 56
Config Check gives no errors
pi@pihole:~ $ unbound-checkconf
unbound-checkconf: no errors in /etc/unbound/unbound.conf
I don't know, but the problem probably lies within "ports already in use". But I can't imagine what causes it, because I tried now many different high ports and the error always appears:
pi@pihole:~ $ unbound -v
[1736517641] unbound[7413:0] notice: Start of unbound 1.17.1.
[1736517641] unbound[7413:0] debug: increased limit(open files) from 1024 to 4140
[1736517641] unbound[7413:0] debug: creating udp4 socket 127.0.0.1 51234
[1736517641] unbound[7413:0] warning: so-rcvbuf 1048576 was not granted. Got 425984. To fix: start with root permissions(linux) or sysctl bigger net.core.rmem_max(linux) or kern.ipc.maxsockbuf(bsd) values.
[1736517641] unbound[7413:0] debug: creating tcp4 socket 127.0.0.1 51234
[1736517641] unbound[7413:0] error: can't bind socket: Address already in use for 127.0.0.1 port 51234 (len 16)
[1736517641] unbound[7413:0] fatal error: could not open ports
Output of opened ports
pi@pihole:~ $ sudo netstat -tulpn | sort -t: -k2 -n
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp6 0 0 ::1:4711 :::* LISTEN 773/pihole-FTL
tcp6 0 0 :::22 :::* LISTEN 696/sshd: /usr/sbin
tcp6 0 0 :::53 :::* LISTEN 773/pihole-FTL
tcp6 0 0 :::80 :::* LISTEN 777/lighttpd
udp6 0 0 :::33348 :::* 545/avahi-daemon: r
udp6 0 0 :::5353 :::* 545/avahi-daemon: r
udp6 0 0 :::53 :::* 773/pihole-FTL
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 696/sshd: /usr/sbin
tcp 0 0 0.0.0.0:53 0.0.0.0:* LISTEN 773/pihole-FTL
udp 0 0 0.0.0.0:53 0.0.0.0:* 773/pihole-FTL
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 777/lighttpd
tcp 0 0 127.0.0.1:4711 0.0.0.0:* LISTEN 773/pihole-FTL
udp 0 0 0.0.0.0:5353 0.0.0.0:* 545/avahi-daemon: r
udp 0 0 0.0.0.0:41866 0.0.0.0:* 545/avahi-daemon: r
tcp 0 0 127.0.0.1:50535 0.0.0.0:* LISTEN 756/stubby
udp 0 0 127.0.0.1:50535 0.0.0.0:* 756/stubby
tcp 0 0 127.0.0.1:51234 0.0.0.0:* LISTEN 7409/unbound
udp 0 0 127.0.0.1:51234 0.0.0.0:* 7409/unbound
Root hints:
; This file holds the information on root name servers needed to
; initialize cache of Internet domain name servers
; (e.g. reference this file in the "cache . <file>"
; configuration file of BIND domain name servers).
;
; This file is made available by InterNIC
; under anonymous FTP as
; file /domain/named.cache
; on server FTP.INTERNIC.NET
; -OR- RS.INTERNIC.NET
;
; last update: December 18, 2024
; related version of root zone: 2024121801
;
; FORMERLY NS.INTERNIC.NET
;
. 3600000 NS A.ROOT-SERVERS.NET.
A.ROOT-SERVERS.NET. 3600000 A 198.41.0.4
A.ROOT-SERVERS.NET. 3600000 AAAA 2001:503:ba3e::2:30
;
; FORMERLY NS1.ISI.EDU
;
. 3600000 NS B.ROOT-SERVERS.NET.
B.ROOT-SERVERS.NET. 3600000 A 170.247.170.2
B.ROOT-SERVERS.NET. 3600000 AAAA 2801:1b8:10::b
;
; FORMERLY C.PSI.NET
;
. 3600000 NS C.ROOT-SERVERS.NET.
C.ROOT-SERVERS.NET. 3600000 A 192.33.4.12
C.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:2::c
;
; FORMERLY TERP.UMD.EDU
;
. 3600000 NS D.ROOT-SERVERS.NET.
D.ROOT-SERVERS.NET. 3600000 A 199.7.91.13
D.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:2d::d
;
; FORMERLY NS.NASA.GOV
;
. 3600000 NS E.ROOT-SERVERS.NET.
E.ROOT-SERVERS.NET. 3600000 A 192.203.230.10
E.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:a8::e
;
; FORMERLY NS.ISC.ORG
;
. 3600000 NS F.ROOT-SERVERS.NET.
F.ROOT-SERVERS.NET. 3600000 A 192.5.5.241
F.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:2f::f
;
; FORMERLY NS.NIC.DDN.MIL
;
. 3600000 NS G.ROOT-SERVERS.NET.
G.ROOT-SERVERS.NET. 3600000 A 192.112.36.4
G.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:12::d0d
;
; FORMERLY AOS.ARL.ARMY.MIL
;
. 3600000 NS H.ROOT-SERVERS.NET.
H.ROOT-SERVERS.NET. 3600000 A 198.97.190.53
H.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:1::53
;
; FORMERLY NIC.NORDU.NET
;
. 3600000 NS I.ROOT-SERVERS.NET.
I.ROOT-SERVERS.NET. 3600000 A 192.36.148.17
I.ROOT-SERVERS.NET. 3600000 AAAA 2001:7fe::53
;
; OPERATED BY VERISIGN, INC.
;
. 3600000 NS J.ROOT-SERVERS.NET.
J.ROOT-SERVERS.NET. 3600000 A 192.58.128.30
J.ROOT-SERVERS.NET. 3600000 AAAA 2001:503:c27::2:30
;
; OPERATED BY RIPE NCC
;
. 3600000 NS K.ROOT-SERVERS.NET.
K.ROOT-SERVERS.NET. 3600000 A 193.0.14.129
K.ROOT-SERVERS.NET. 3600000 AAAA 2001:7fd::1
;
; OPERATED BY ICANN
;
. 3600000 NS L.ROOT-SERVERS.NET.
L.ROOT-SERVERS.NET. 3600000 A 199.7.83.42
L.ROOT-SERVERS.NET. 3600000 AAAA 2001:500:9f::42
;
; OPERATED BY WIDE
;
. 3600000 NS M.ROOT-SERVERS.NET.
M.ROOT-SERVERS.NET. 3600000 A 202.12.27.33
M.ROOT-SERVERS.NET. 3600000 AAAA 2001:dc3::35
; End of file
Unbound Conf:
server:
# If no logfile is specified, syslog is used
logfile: "/var/log/unbound/unbound.log"
verbosity: 4
interface: 127.0.0.1
port: 51234
do-ip4: yes
do-udp: yes
do-tcp: yes
# May be set to yes if you have IPv6 connectivity
do-ip6: yes
# You want to leave this to no unless you have *native* IPv6. With 6to4 and
# Terredo tunnels your web browser should favor IPv4 for the same reasons
prefer-ip6: yes
# Use this only when you downloaded the list of primary root servers!
# If you use the default dns-root-data package, unbound will find it automatically
root-hints: "/var/lib/unbound/root.hints"
# Trust glue only if it is within the server's authority
harden-glue: yes
# Require DNSSEC data for trust-anchored zones, if such data is absent, the zone becomes BOGUS
harden-dnssec-stripped: yes
# Don't use Capitalization randomization as it known to cause DNSSEC issues sometimes
# see https://discourse.pi-hole.net/t/unbound-stubby-or-dnscrypt-proxy/9378 for further details
use-caps-for-id: no
# Reduce EDNS reassembly buffer size.
# IP fragmentation is unreliable on the Internet today, and can cause
# transmission failures when large DNS messages are sent via UDP. Even
# when fragmentation does work, it may not be secure; it is theoretically
# possible to spoof parts of a fragmented DNS message, without easy
# detection at the receiving end. Recently, there was an excellent study
# >>> Defragmenting DNS - Determining the optimal maximum UDP response size for DNS <<<
# by Axel Koolhaas, and Tjeerd Slokker (https://indico.dns-oarc.net/event/36/contributions/776/)
# in collaboration with NLnet Labs explored DNS using real world data from the
# the RIPE Atlas probes and the researchers suggested different values for
# IPv4 and IPv6 and in different scenarios. They advise that servers should
# be configured to limit DNS messages sent over UDP to a size that will not
# trigger fragmentation on typical network links. DNS servers can switch
# from UDP to TCP when a DNS response is too big to fit in this limited
# buffer size. This value has also been suggested in DNS Flag Day 2020.
edns-buffer-size: 1232
# Perform prefetching of close to expired message cache entries
# This only applies to domains that have been frequently queried
prefetch: yes
# One thread should be sufficient, can be increased on beefy machines. In reality for most users running on small networks or on a single machine, it should be unnecessary to seek performance enhancement by increasing num-threads above 1.
num-threads: 1
# Ensure kernel buffer is large enough to not lose messages in traffic spikes
so-rcvbuf: 1m
# Ensure privacy of local IP ranges
private-address: 192.168.0.0/16
private-address: 169.254.0.0/16
private-address: 172.16.0.0/12
private-address: 10.0.0.0/8
private-address: fd00::/8
private-address: fe80::/10
Debug Token:
https://tricorder.pi-hole.net/KhNoqnUh/
Some tips would be nice, thanks