Yes.
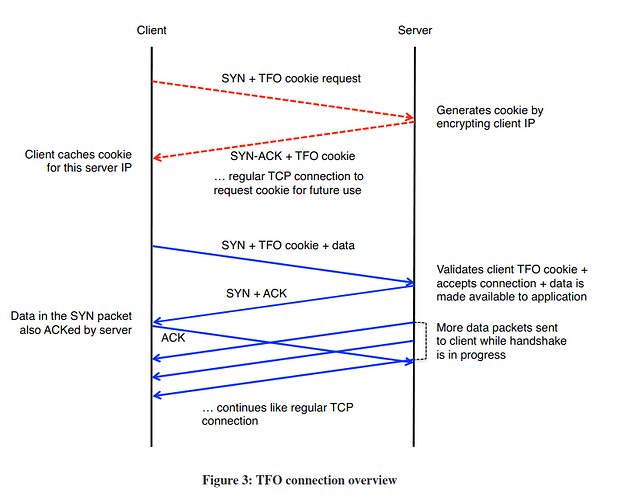
The current dnsmasq always requests TCPFO for incoming and outgoing TCP connections. The kernel will automatically do the rest (it may even ignore this request if TCPFO is not enabled, see below). The use of TCPFO cookies is transparent to the application level: the TCPFO cookie is automatically generated during the first TCP conversation between the client and server, and then automatically reused in subsequent conversations if TCPFO is enabled.
To prevent resource-exhaustion attacks, one of the potential issues with TCPFO, dnsmasq sets the limit on the size of the queue of TCPFO requests that have not yet completed the three-way handshake to 5.
You can check by issuing cat /proc/sys/net/ipv4/tcp_fastopen
If this value is 0, then TCPFO is disabled.
If it is 1, then TCPFO is in client-mode (outgoing), i.e., you can use TCPFO to connect to others servers which support it (technically: you can read a TCPFO cookie).
If it is 2, then TCPFO is in server-mode (incoming), i.e., others can connect to your server using TCPFO (technically: you can generate TCPFO cookies for others).
If the values is 3, you can use both and TCPFO is fully enabled (incoming and outgoing).
You can set the value yourself using, e.g.,
echo "3" | sudo tee /proc/sys/net/ipv4/tcp_fastopen
to fully enable TCPFO.
According to the kernel sysctl ip documentation, the default is enabled client support (value 1).
Nothing. The kernel code uses the net/ipv4/tcp_fastopen value for all TCP connections, regardless of the used protocol. See the corresponding kernel code if you are interested (this subroutine is used from ../ipv6/tcp_ipv6.c as well).
I'm aware that this is somewhat misleading. TCPFO-IPv6 support was added in a later kernel version than TCPFO-IPv4 support, so I assume the IPv6 implementer simply did a minimal effort implementation, not wanting to touch the existing settings (this is a bigger deal). Plus. there is no obvious reason to have different behavior for TCP with IPv4 and IPv6.
It seems this conclusion is a bit extreme. I would not say this.
The "danger" is that the source could be spoofed. Well, this can be done much easier with UDP as well. I do not see this being a danger at all for DNS servers. As dnsmasq has both a limit on concurrent TCP connections and on the queue of TCPFO requests, I can hardly see any danger for a DDoS attack here (which is what you typically want to achieve with source IP spoofing).