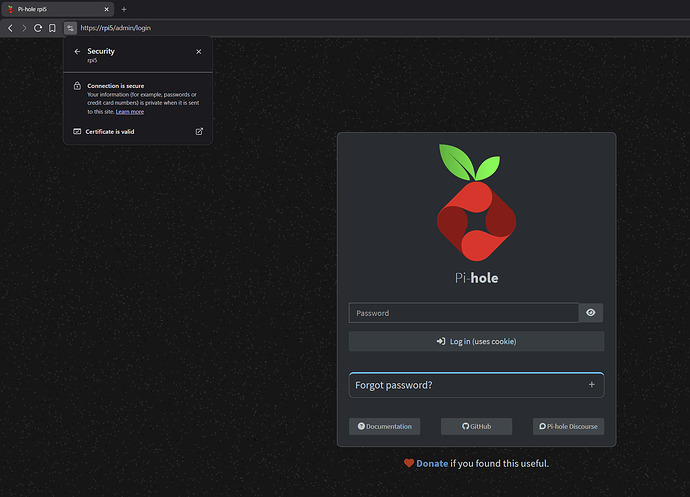
Local HTTPS for Pi-hole (previously "pihole-https") 
Hello everyone,
Some time ago I shared a small script called pihole-https to enable HTTPS on the Pi-hole web interface with minimal manual TLS setup.
Based on community feedback and further development, the project has evolved and is now called local-https.
Despite the new name, Pi-hole remains a primary and fully supported use case.
The rename reflects an internal redesign and a more robust certificate management model, not a change in focus.
What local-https does for Pi-hole
local-https automates HTTPS for the Pi-hole web interface by:
-
Creating (or reusing) a local Root Certificate Authority
-
Issuing short-lived HTTPS certificates
-
Automatically renewing certificates before expiration
-
Automatically deploying renewed certificates to Pi-hole
-
Reloading the correct Pi-hole web service (FTL or Lighttpd)
Once the local Root CA is trusted on your devices, the Pi-hole web UI can be accessed over HTTPS without browser warnings.
Supported on Debian-based distributions (Debian, Ubuntu, Raspberry Pi OS, Armbian).
Other distributions may work but are not officially supported.
About certificate lifetime (40 days)
Thanks to @nero355 for previously pointing out the industry shift toward shorter TLS certificate lifetimes.
Modern browser and CA policies are moving away from long-lived certificates in favor of ~40–45 day validity periods, improving security and reducing the impact of key compromise.
local-https follows this model and relies on automatic renewal, so the shorter lifetime does not add operational overhead.
Reference:
Repository
The project is open source and available here:
The README covers:
-
Installation and uninstall instructions
-
Automatic renewal details
-
Pi-hole-specific integration notes
-
Device trust instructions for Windows, macOS, Linux, Android, and iOS
Installation
The project provides a simple one-step installer:
curl -fsSL https://raw.githubusercontent.com/luizbizzio/local-https/main/install.sh | sudo bash
This installs the local-https command and guides you through the setup, including optional automatic renewal via systemd.
Notes
-
It uses OpenSSL, not Let's Encrypt
-
This uses a local Root CA and is intended for private networks
-
It is not designed for public HTTPS or for use inside Docker containers
-
Feedback and suggestions are welcome
Thanks to the Pi-hole community for the discussions and feedback that helped shape this update.