Hope I'm wrong (logic error?) but...
Like a lot of you, I've implemented a NAT rule, redirecting all DNS queries, not originating from pihole. We all know this happens (android, chromecast, nvidia shield, ...), so once it works, we never look back (I didn't).
In order to get a clear picture of the culprits, I've added something to my pihole to be able to log these redirections, full manual (how to) here (pfsense + pihole-FTL + dnsmasq).
Looks like it works, the devices mentioned above all try to bypass pihole, the queries are logged (by the additional dnsmasq - NOT listening on port 53) and eventually replied to by pihole.
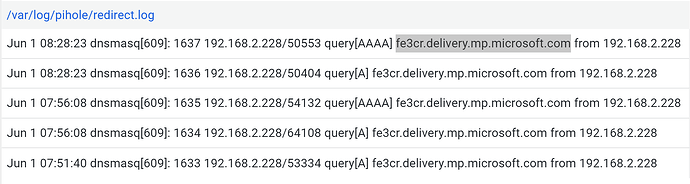
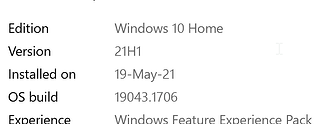
Today, however (192.168.2.228 is a windows 10 laptop):
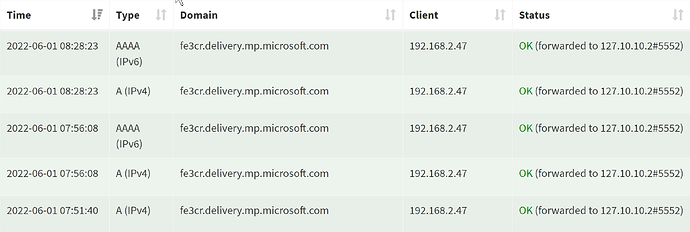
thus redirected to pihole (all redirected requests arrive from the secondary IP address 192.168.2.47)
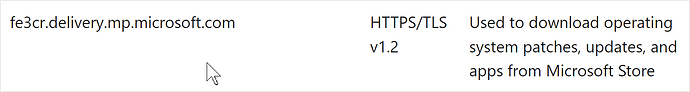
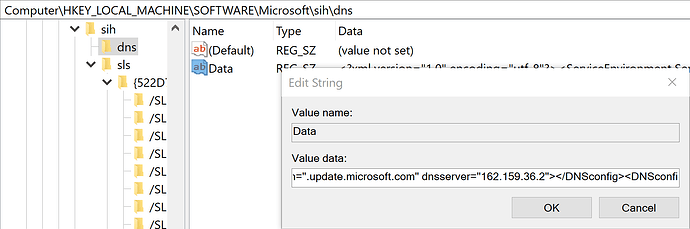
I checked, before today, all the requests for the domain fe3cr.delivery.mp.microsoft.com went straight to pihole (no attempt to bypass), however, as of this morning, these queries (only for the above mentioned domain) attempted to bypass pihole.
Unfortunately, pfsense doesn't have a logging option on NAT rules, so I have no idea where these requests would like to get a reply from (the original query -> NS target).
I haven't installed anything additional on the laptop recently, so this has to come from something that was already installed, behaved as it should (use configured DNS server) and changed it's behaviour (trying to bypass) today.