HELLO,
I want to share dnscrypt-proxy-pihole
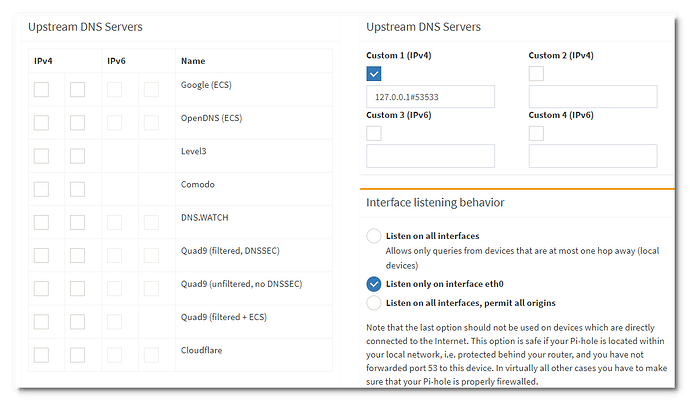
It is a debian package for Raspberry Pi which installs dnscrypt-proxy configured for DNS over HTTPS with Cloudflare DNS servers and Pi-hole.
Isp can still see what domains you go to ![]()
Use VPN
@anon55913113 Why?
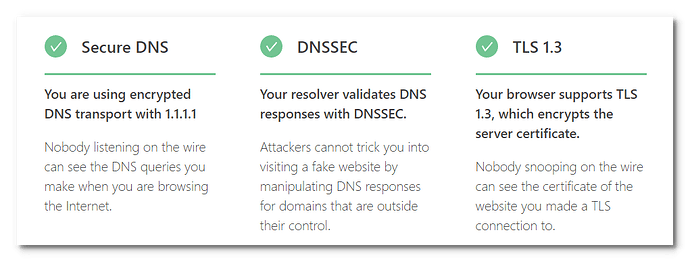
@anon55913113 Traditionally, DNS queries are sent in plaintext. Anyone listening on the Internet can see which websites you are connecting to. To ensure your DNS queries remain private, you should use a resolver that supports secure DNS transport such as DNS over HTTPS (DoH) or DNS over TLS (DoT).
After you get the encrypted DNS transaction completed and have the IP in hand, you immediately send that IP to your ISP in clear text and request that they connect you. It is not difficult for the ISP to figure out where you are browsing.
If you use a VPN service they see the same.
They have it to inspect.
hi. when you suggest 'use vpn' do you (anyone please) mean something like this:
also, i suscribe to a vpn service which i can code into my router (open vpn client) w/ ovpn files, etc. from my vpn provider.
anyway, the merlin firnware router has policy rules for how you might like to route traffic thruogh the vpn.
ex:
so just wondering, if i want to encrypt my pihole and unbound activity properly through the vpn that is, would i use that?
that is, in the 'source' if i add my pihole ip, add the destination ip as 0.0.0.0 lface set to vpn...
Setup: dnscrypt-proxy-pihole_2.0.44; Pi-hole v5.1.2; RPi 4B, 4GB. I am also running log2ram
I followed the instructions and on executing this:
sudo dpkg -i dnscrypt-proxy-pihole_2.0.44_armhf.deb; apt install -f -y
I am getting this:
(Reading database ... 118347 files and directories currently installed.)
Preparing to unpack dnscrypt-proxy-pihole_2.0.44_armhf.deb ...
Unpacking dnscrypt-proxy-pihole (2.0.44) over (2.0.44) ...
Setting up dnscrypt-proxy-pihole (2.0.44) ...
adduser: Only one or two names allowed.
dpkg: error processing package dnscrypt-proxy-pihole (--install):
installed dnscrypt-proxy-pihole package post-installation script subprocess returned error exit status 1
Errors were encountered while processing:
dnscrypt-proxy-pihole
E: Could not open lock file /var/lib/dpkg/lock-frontend - open (13: Permission denied)
E: Unable to acquire the dpkg frontend lock (/var/lib/dpkg/lock-frontend), are you root?
I tried again with sudo su and this time I am getting the same 'Please choose...' menu twice and the following errors:
(Reading database ... 118347 files and directories currently installed.)
Preparing to unpack dnscrypt-proxy-pihole_2.0.44_armhf.deb ...
Unpacking dnscrypt-proxy-pihole (2.0.44) over (2.0.44) ...
Setting up dnscrypt-proxy-pihole (2.0.44) ...
adduser: Only one or two names allowed.
dpkg: error processing package dnscrypt-proxy-pihole (--install):
installed dnscrypt-proxy-pihole package post-installation script subprocess returned error exit status 1
Errors were encountered while processing:
dnscrypt-proxy-pihole
Reading package lists... Done
Building dependency tree
Reading state information... Done
0 upgraded, 0 newly installed, 0 to remove and 0 not upgraded.
1 not fully installed or removed.
After this operation, 0 B of additional disk space will be used.
Setting up dnscrypt-proxy-pihole (2.0.44) ...
adduser: Only one or two names allowed.
dpkg: error processing package dnscrypt-proxy-pihole (--configure):
installed dnscrypt-proxy-pihole package post-installation script subprocess returned error exit status 1
Errors were encountered while processing:
dnscrypt-proxy-pihole
E: Sub-process /usr/bin/dpkg returned an error code (1)
Any advice please?
sudo dpkg -i dnscrypt-proxy-pihole_2.0.44_armhf.deb; sudo apt install -f -y
Thanks for the quick response. This corresponds to the second case above. I am getting the menu twice and the error below.
$ sudo dpkg -i dnscrypt-proxy-pihole_2.0.44_armhf.deb; sudo apt install -f -y
(Reading database ... 118347 files and directories currently installed.)
Preparing to unpack dnscrypt-proxy-pihole_2.0.44_armhf.deb ...
Unpacking dnscrypt-proxy-pihole (2.0.44) over (2.0.44) ...
Setting up dnscrypt-proxy-pihole (2.0.44) ...
adduser: Only one or two names allowed.
dpkg: error processing package dnscrypt-proxy-pihole (--install):
installed dnscrypt-proxy-pihole package post-installation script subprocess returned error exit status 1
Errors were encountered while processing:
dnscrypt-proxy-pihole
Reading package lists... Done
Building dependency tree
Reading state information... Done
0 upgraded, 0 newly installed, 0 to remove and 0 not upgraded.
1 not fully installed or removed.
After this operation, 0 B of additional disk space will be used.
Setting up dnscrypt-proxy-pihole (2.0.44) ...
adduser: Only one or two names allowed.
dpkg: error processing package dnscrypt-proxy-pihole (--configure):
installed dnscrypt-proxy-pihole package post-installation script subprocess returned error exit status 1
Errors were encountered while processing:
dnscrypt-proxy-pihole
E: Sub-process /usr/bin/dpkg returned an error code (1)
Please download new deb package.
- Fixed missing user _dnscrypt-proxy
This worked just fine. Many thanks.
Updated to version 2.0.45
https://github.com/mapi68/dnscrypt-proxy-pihole
How? Up till now what I had read claims they can't, if we use DoH/DoT and HTTPS.
Could u point some article explaining how it can be leaked?
VPN protects from ISP, but opens us to privacy issues regarding VPN provider.
The advantage is that, on web, some sites don't support HTTPS. So we use HTTP and ISP sees whole HTTP message and the domain on HTTP header.
And HTTPS is useless for all services that aren't using web. VPN can be used on anything, specially when it's set on OS level or on the router.
In general, I don't see VPN and DoH as competitors.
DoH doesn't seem to aim to replace VPN, in the situation of just providing another level of privacy.
VPN tunnels everything, all ISP sees is that the user keeps accessing the same IP (VPN server) and nothing else. If user is being seriously monitored, it's easy for ISP to block that VPN server and bring the user down. VPN traffic is also easy to be identified.
DoH/DoT + HTTPS doesn't make we rely on a single party, at least not more than we rely on a public DNS service provider. DoH looks like normal HTTPS messages, but always going to the same IP, which with a few inspection is easy to identify as a DNS server and therefore all those HTTPS-looking messages as DoH. Still, it's very unprobeable for a ISP to bother with that.
If ad services aren't bothering with their domains being blocked on DNS level, normal ISPs will never bother with users using DoH.
If the issue isn't a simple privacy concern, then for sure DoH will not be a solution, and maybe VPN won't either.
That's another point. Cloud services and also shared hosts. With current hardware, a single server (IP) can serve over a thousand customers and many thousands small websites. ISP can know by the IP when we access big websites and portals, but for small ones they will have trouble even to figure out the host company. It's virtually impossible to know the website/domain without snuffing on the HTTP message.
You may have hid the fact that you wanted to know the IP of domain.com is, but you tell the ISP the IP address you are going to. That's just how TCP/IP works. And all the hops along the route know your IP and the IP you are headed for.
No, it's really not.
Updated to version 2.0.46 BETA 3
Updated to version 20210802
Updated to version 20211007