Apologies - didn't get chance to pick this up again until now.
Networking in general isn't my strong point so I'll try and provide as much information as I can that seems it might be relevant.
The PI has two NICs - the build in ethernet, which is eth0, and handles the lan side of the network. The second NIC is a USB adapter - eth1 - which handles the wan via a connection to a DSL modem in bridge mode. The PI itself authenticates and obtains the wan IP.
This is the output of ifconfig for eth0 and eth1:
eth0: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.0.1 netmask 255.255.255.0 broadcast 192.168.0.255
inet6 xxxxxxx prefixlen 64 scopeid 0x20<link>
ether XX:XX:XX:XX:XX:XX txqueuelen 1000 (Ethernet)
RX packets 14010 bytes 1684344 (1.6 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 22796 bytes 26779794 (25.5 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
eth1: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 2.XXX.X.3 netmask 255.255.252.0 broadcast 2.XXX.X.255
inet6 xxxxxxx prefixlen 64 scopeid 0x20<link>
ether XX:XX:XX:XX:XX:XX txqueuelen 1000 (Ethernet)
RX packets 33160 bytes 41412493 (39.4 MiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 19050 bytes 2059954 (1.9 MiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
This is the routing table for the Pi:
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
0.0.0.0 2.XXX.X.1 0.0.0.0 UG 203 0 0 eth1
2.XXX.X.0 0.0.0.0 255.255.252.0 U 203 0 0 eth1
169.254.0.0 0.0.0.0 255.255.0.0 U 203 0 0 eth1
192.168.0.0 0.0.0.0 255.255.255.0 U 202 0 0 eth0
So, as I understand it, lan traffic is routed internally. Any wan traffic takes the default route (the top line of the routing table).
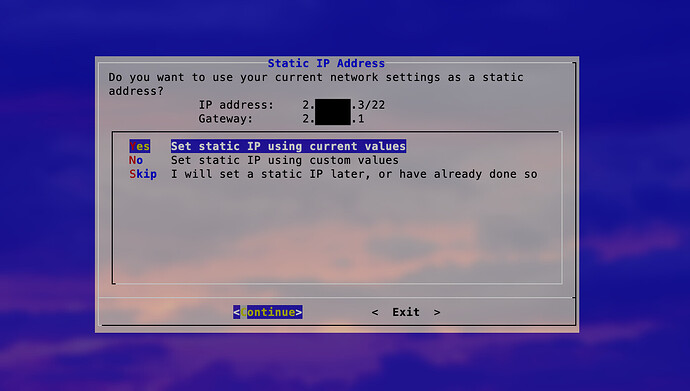
At this point - before I installed isc-dhcp-server - so there was no DHCP server at all running on the Pi - when I installed Pi-hole I selected eth0 as the adapter that Pi-hole would listen on. The default IP for that adapter, rather than 192.168.0.1, was the wan IP. At this point I don't know what the gateway should be, as there is no gateway configured on eth0, and eth1 is not a static IP as it's provided by the ISP. When I've installed Pi-hole in the past with a separate router, the static IP of the relevant NIC is the default, along with the gateway which is the router IP.
Whatever I enter for the gateway value here, when Pi-hole completes the install, eth0 has lost the 192.168.0.1 IP completely. At that point all clients lose connectivity to the Pi.
The IP of eth0 is assigned in the config file for the adapter - not by DHCP:
interface eth0
static ip_address=192.168.0.1/24
static routers=192.168.0.1
static domain_name_servers=192.168.0.1
nogateway
Hopefully that's a bit clearer. Happy to post firewalld and isc-dhcp-server configs but I don't believe they are part of this issue, which seems related to the routing and / or NIC config.
TIA
Si