My versions:
- Core v6.3
- FTL v6.4.1
- Web interface v6.4
My PiHole is running on a raspberry pi 2 without container.
My network have two network interface:
- vlan@eth0 : ULA IPv6 prefix, no IPv4
- eth0 : global IPv6 prefix, private IPv4
With IPv6, you can mix slaac and manual configuration. This allow to have a dedicated IP address for DNS listening in the form: ::53 . This is what we can call a service address.
In my case, the raspberry by have both a global service address and an ULA service address so it have a total of 7 IP addresses.
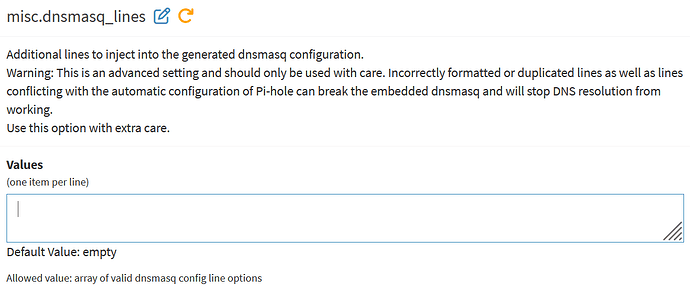
FTL interface setting does not allow to select interfaces and addresses to bind to
Listening on all addresses of all interfaces is not considered as a good practice for a while.
As id do with bind or ssh or any other network service, i want to restrict FTL bind to a specific list of addresses.
Issue with network interfaces
Even when telling to bind to eth0 only, FTL bind to the vlan network interface : this should not be the case. So this is a bug for me.
Issue with network addresses
Link local: FTL should never bind to either IPv4 or IPv6 link local addresses because resolution is then the mDNS business with .local names.
When several IP addresses are present, FTL should allow to select the addresses it should bind to : In my case, only DNS service addresses.
My dream: make FTP no longer bind to the IPv4 address because DHCP will be shutdown soon.