It would be nice if this LAN DNS server (lan.list) solution could support wildcard. e.g. *.mydomain.com
Now I have to enter every sub-domain manually every time I create a sub-domain or change something.
I have a wildcard SSL so it would be useful.
Do you really do this as often? If so, why? How should such a support look like? Will all the subdomains you create point to the same IP address?
No I don’t change that often my sub-domains. I guess you could say that I’m a bit spoilt because my DNS server on my Synology NAS has the ability to use a wildcard. So I didn’t have to manually entered all the sub-domains that I use at the moment.
Most of the sub-domains point to the same IP address. Some I’m using when testing something on my virtual-machine.
I’m guessing it would be more of a convenient thing than a must.
Maybe it would be a better idea to implement this in the webadmin?
So that one could enter the LAN information through the GUI.
Maybe this is an idea to implement in a pi-hole future version?
I'm testing Adguard at the moment vs pi-hole, any I must say the configuration for (lan)domains is much easier.
@BobWs Do you have some screenshots, maybe alongside a description of what is what for us?
I'll try to explain ![]()
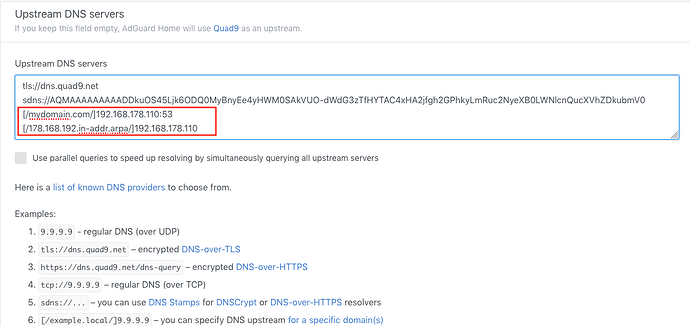
Here's a screenshot of my Adguard DNS config. As you can see I have entered:
[/mydomain.local/]192.168.178.110:53
[/178.168.192.in-addr.arpa/]192.168.178.110
And because I have a DNS server running on my Local network I do not have to enter every single client or "sub.domain.local" manually in to the pihole/lan.list.
I guess this will only work and be useful if one has it's own DNS server running locally.
Reference Adguard site:
If one or more domains are specified, that upstream (upstreamString) is used only for those domains. Usually, it is used for private nameservers.
For instance, if you have a nameserver on your network which deals with xxx.internal.local at 192.168.0.1 then you can specify[/internal.local/]192.168.0.1, and AdGuard Home will send all queries to that nameserver.
Everything else will be sent to the default upstreams (which are mandatory!).
An empty domain specification, // has the special meaning of "unqualified names only" ie names without any dots in them.
More specific domains take precedence over less specific domains, so: [/host.com/]1.2.3.4 + [/www.host.com/]2.3.4.5 will send queries for *.host.com to 1.2.3.4, except *.www.host.com, which will go to 2.3.4.5
The special server address '#' means, "use the standard servers", so: [/host.com/]1.2.3.4 + [/www.host.com/]# will send queries for *.host.com to 1.2.3.4, except *.www.host.com which will be forwarded as usual.
Seems the feature itself is provided by dnsmasq:
The referenced text been taken from dnsmasq's man pages almost verbatim - check the -S, --local, --server option section.
As dnsmasq is embedded in Pi-hole, you could supply those values in a custom dnsmasq configuration file straight away.
I agree and this has long (read as in "forever") been supported by custom configuration files. However, adding it in the form AdGuard allows it (free-text field) seems dangerous to me. A single mistyped character can cause the entire DNS server to fail (dnsmasq won't start with config file typos).
We have discussed this (often) in the past, but it's never a bad idea to revisit things after a while to see if the situation has changed. I still think we should make the user interface as easy as possible for the inexperienced. I think we've already gone a bit beyond this in some places, but adding a multiline text field and telling people that a specific syntax is needed just seems to be a loose and lazy things to do. Power users can go to custom files in /etc/dnsmasq.d/ and we did and will always provide support for such custom configs.
I see ![]()
I will give it a try
Can't seem to get it to work?!
I have add 02-nameservers.conf to /etc/dnsmasq.d/
with this value in the file: addn-hosts=/etc/pihole/nameservers.list
then I have created a file within /etc/pihole /etc/pihole/nameservers.list and I have entered thiss value in the file: --server=/mydomain.local/192.168.178.110
After this I restarted pi-hole(beta) and tried to go to a subdomain wich isn't specified in the customlist but it isn't working. The page isn't loading I get a errorpage.
When I enter the subdomain in the customlist then the page is loading.
You should put
server=/mydomain.local/192.168.178.110
(note the absence of --) directly into 02-nameservers.conf.
Is 192.168.178.110 running a DNS server? Note that your configuration specifies to ask this server for any *.mydomain.local domains. It does not say that any subdomain on mydomain.local has said IP address. (It doesn't appear to mean this for Adguard, either, guessing from the description in your screenshot above).
When you specify
addn-hosts=/etc/pihole/nameservers.list
this list does only contain host records, i.e.,
ip hostname
cfm. dnsmasq's man page:
-H, --addn-hosts=<file>Additional hosts file. Read the specified file as well as
/etc/hosts. If--no-hostsis given, read only the specified file. This option may be repeated for more than one additional hosts file. If a directory is given, then read all the files contained in that directory.
Thanks! It is working ![]()
I have change as you suggested the 02-nameservers.conf file
and add the following
server=/mydomain.local/192.168.178.110
server=/178.168.192.in-addr.arpa/192.168.178.110
directly into the 02-nameservers.conf file and it is working!
Okay, very nice. As said, you can do a lot with Pi-hole, I'm not sure we should offer everything on the dashboard. Most often, it is better to discuss things so we can find the optimal solution together with the more experienced users. It would also not have been the first time a user asked for something he doesn't actually wanted (because they were not sure how to achieve something best). I'm pretty sure we always came to a good solution for everyone here*.
*) Except maybe those demanding DNSoverHTTPS or DNSoverTLS becoming directly integrated into FTL. We still support them with stuby or unbound or whatever solution you prefer even on the same machine.
Thanks m8 for clarifying and explaining the extra features of Pi-hole. Because of missing this feature I had already switched to Adguard, but now that I've been able to apply it I can make full use of this fantastic program again.
In the future I will first ask my question here if I doubt if pihole offers certain possibilities I can't find myself.