By now, I know how much you hate any configuration, deviating from what the developers originally intended, which is buster on raspberry pi + pihole install + optionally unbound, nothing more.
Although I understand, from a point of providing support, the reason for this, there will always be users, wanting more sophisticated features, be it for the simple reason that it's possible.
I'm also very aware you don't like the redis solution, and don't want to support it.
To eliminate this discussion, I've done the following:
- stopped unbound, redis and pihole-FTL
- /etc/dnsmasq.d/01-pihole.conf, cache-size=10000
- removed logs and pihole-FTL.db
- removed redis config file from unbound (config is a separate file, by removing it unbound will no longer attempt to use it)
- restarted unbound and pihole-FTL, did NOT restart redis (no longer in use), all stats in pihole dashboard are now zero.
- rebooted two out of three windows machines.
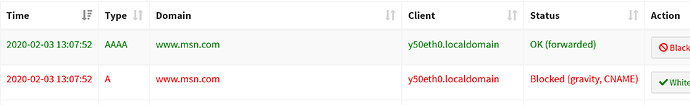
Within minutes, I noticed the following:
I know, you'll probably still be sceptic about my config, for me, this proves it has nothing to do with redis.
Please accept my apologies if I have somehow offended you, this is absolutely NOT my intention. Just want to assist to get a bug free version of pihole v5.