Hi there.
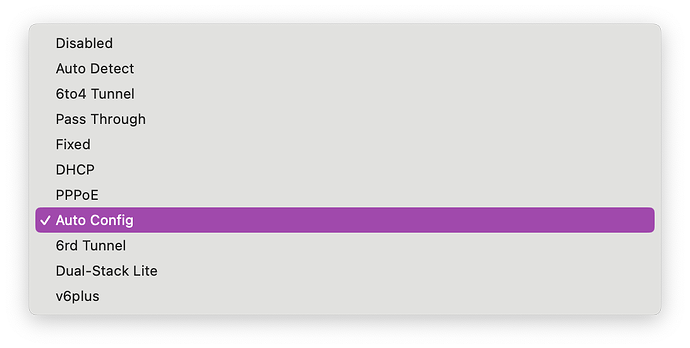
I am running Pi-hole on a Raspberry Pi 3 in a non-unusual setup. I have a Netgear Nighthawk RAX200 Wi-Fi 6 router that I've had since late 2020. I have been successfully using Pi-hole since December 2022 to block out ads, which has made browsing the web a much more pleasant experience. The router is the DHCP server, it has the Pi's wlan0 interface (used for Pi-hole) set to a static IPv4 address, and it has IPv6 enabled.
However, I noticed today that my ad blocking isn't working. It appears to be related to IPv6. I provide a value for primary (not secondary) DNS in the IPv6 section, yet all clients on my network report these additional DNS servers:
2001:558:feed::1
2001:558:feed::2
These appear to be the default IPv6 DNS servers for Comcast, my ISP.
I have no idea why these DNS servers are being propagated to each of my devices. I know these are defaults, but my assumption is that by setting a custom DNS server, it should override any ISP-provided DNS servers, and this matches behavior I was experiencing before today.
To isolate, I have even tried setting both primary and secondary IPv6 DNS servers to CloudFlare's and clearing out my Pi-hole's IPv6 DNS entirely, but both Comcast IPv6 DNS servers still come down to other devices.
Unfortunately, this problem effectively defeats Pi-hole entirely since the ads/trackers will find their way around using the Comcast IPv6 DNS servers.
I have tried contacting both Comcast and Netgear support. Both companies have proven equally frustrating and unhelpful.
I've already taken a look at similar issues, and it seems the only thing that has worked for these folks is to disable IPv6 altogether. However, this seems undesirable and only a last resort if the root cause of the extra DNS server propagation cannot be determined or fixed.
I am not well versed in IPv6 or the mechanics of what would cause default ISP DNS servers to be sent to clients even despite custom DNS being set.
Goals:
- To determine why the ISP DNS servers are being forced to clients
- Fix or eliminate this and force router to only use Pi-hole as DNS server (IPv6)
- To avoid disabling IPv6 if possible
Expected Behaviour:
Devices on my network inherit only DNS servers that I've custom defined in my router for both IPv4 and IPv6.
Actual Behaviour:
I receive additional unexpected IPv6 DNS servers on clients, thus defeating Pi-hole entirely.
Debug Token:
L3i3YT6X
Thanks for reading and I appreciate any help!