Please follow the below template, it will help us to help you!
Expected Behaviour:
[Replace this text with what you think should be happening]
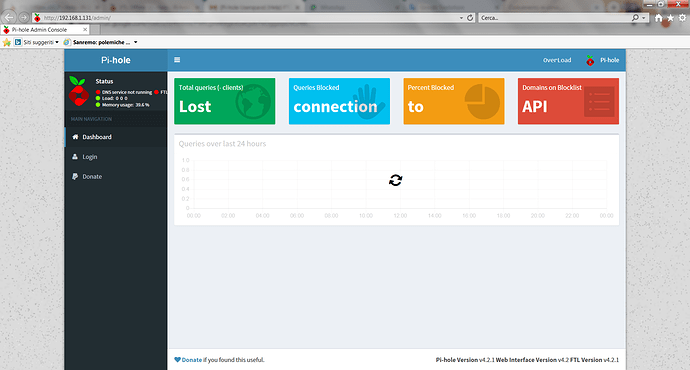
Actual Behaviour:
[replace this text with what is actually happening]
Debug Token:
[Replace this text with the debug token provided from running pihole -d (or running the debug script through the web interface]
This process collects information from your Pi-hole, and optionally uploads it to a unique and random directory on tricorder.pi-hole.net.
The intent of this script is to allow users to self-diagnose their installations. This is accomplished by running tests against our software and providing the user with links to FAQ articles when a problem is detected. Since we are a small team and Pi-hole has been growing steadily, it is our hope that this will help us spend more time on development.
NOTE: All log files auto-delete after 48 hours and ONLY the Pi-hole developers can access your data via the given token. We have taken these extra steps to secure your data and will work to further reduce any personal information gathered.
*** [ INITIALIZING ]
[i] 2019-02-10:20:37:57 debug log has been initialized.
*** [ INITIALIZING ] Sourcing setup variables
[i] Sourcing /etc/pihole/setupVars.conf...
*** [ DIAGNOSING ]: Core version
[i] Core: v4.2.1 (https://discourse.pi-hole.net/t/how-do-i-update-pi-hole/249)
[i] Branch: master
[i] Commit: v4.2.1-0-ge967fe2
*** [ DIAGNOSING ]: Web version
[i] Web: v4.2 (https://discourse.pi-hole.net/t/how-do-i-update-pi-hole/249)
[i] Branch: master
[i] Commit: v4.2-0-g347994db
*** [ DIAGNOSING ]: FTL version
[✓] FTL: v4.2.1
*** [ DIAGNOSING ]: lighttpd version
[i] 1.4.45
*** [ DIAGNOSING ]: php version
[i] 7.0.33
*** [ DIAGNOSING ]: Operating system
[✓] Raspbian GNU/Linux 9 (stretch)
*** [ DIAGNOSING ]: SELinux
[i] SELinux not detected
*** [ DIAGNOSING ]: Processor
[✓] armv7l
*** [ DIAGNOSING ]: Networking
[✓] IPv4 address(es) bound to the eth0 interface:
192.168.1.131/24 matches the IP found in /etc/pihole/setupVars.conf
[✓] IPv6 address(es) bound to the eth0 interface:
fe80::976c:5ffd:69fe:13a does not match the IP found in /etc/pihole/setupVars.conf (https://discourse.pi-hole.net/t/use-ipv6-ula-addresses-for-pi-hole/2127)
^ Please note that you may have more than one IP address listed.
As long as one of them is green, and it matches what is in /etc/pihole/setupVars.conf, there is no need for concern.
The link to the FAQ is for an issue that sometimes occurs when the IPv6 address changes, which is why we check for it.
[i] Default IPv4 gateway: 192.168.1.1
* Pinging 192.168.1.1...
[✓] Gateway responded.
*** [ DIAGNOSING ]: Ports in use
[::1]:631 cupsd (IPv6)
127.0.0.1:631 cupsd (IPv4)
[*:53] is in use by pihole-FTL
[127.0.0.1:53] is in use by pihole-FTL
[10.8.0.1:53] is in use by pihole-FTL
127.0.0.1:953 named (IPv4)
[::1]:953 named (IPv6)
[192.168.1.131:53] is in use by pihole-FTL
*:5900 vncserver- (IPv6)
*:5900 vncserver- (IPv4)
*:22 sshd (IPv4)
*:22 sshd (IPv6)
127.0.0.1:3306 mysqld (IPv4)
*:9999 apache2 (IPv6)
*:8888 rpimonitor (IPv4)
*:9999 apache2 (IPv6)
*:9999 apache2 (IPv6)
*:9999 apache2 (IPv6)
*:9999 apache2 (IPv6)
*:9999 apache2 (IPv6)
*:445 smbd (IPv6)
*:139 smbd (IPv6)
*:445 smbd (IPv4)
*:139 smbd (IPv4)
*:10000 miniserv.p (IPv4)
*:6001 Xvnc-core (IPv6)
*:6001 Xvnc-core (IPv4)
*:5901 Xvnc-core (IPv6)
*:5901 Xvnc-core (IPv4)
[*:80] is in use by lighttpd
[*:80] is in use by lighttpd
*** [ DIAGNOSING ]: Name resolution (IPv4) using a random blocked domain and a known ad-serving domain
[✓] howler.shareaholic.com is 54.173.180.162
52.20.72.246 via localhost (127.0.0.1)
[✓] howler.shareaholic.com is 52.20.72.246
54.173.180.162 via Pi-hole (192.168.1.131)
[✓] doubleclick.com is 216.58.198.46 via a remote, public DNS server (8.8.8.8)
*** [ DIAGNOSING ]: Pi-hole processes
[✓] lighttpd daemon is active
[✓] pihole-FTL daemon is active
*** [ DIAGNOSING ]: Setup variables
BLOCKING_ENABLED=true
DNSMASQ_LISTENING=single
PIHOLE_DNS_3=208.67.222.222
PIHOLE_DNS_4=208.67.220.220
DNS_FQDN_REQUIRED=true
DNS_BOGUS_PRIV=true
DNSSEC=false
CONDITIONAL_FORWARDING=false
API_EXCLUDE_DOMAINS=
API_EXCLUDE_CLIENTS=192.168.1.111,192.168.1.109,192.168.1.2,192.168.1.3,192.168.1.110,192.168.1.112
API_QUERY_LOG_SHOW=all
API_PRIVACY_MODE=false
PIHOLE_INTERFACE=eth0
IPV4_ADDRESS=192.168.1.131/24
IPV6_ADDRESS=
PIHOLE_DNS_1=8.8.8.8
PIHOLE_DNS_2=8.8.4.4
QUERY_LOGGING=true
INSTALL_WEB_SERVER=true
INSTALL_WEB_INTERFACE=true
LIGHTTPD_ENABLED=true
*** [ DIAGNOSING ]: Dashboard and block page
[✗] Block page X-Header: X-Header does not match or could not be retrieved.
HTTP/1.1 200 OK
Content-Type: text/html
Accept-Ranges: bytes
ETag: "3909837145"
Last-Modified: Sat, 22 Sep 2018 19:05:08 GMT
Content-Length: 10701
Date: Sun, 10 Feb 2019 19:38:06 GMT
Server: lighttpd/1.4.45
[✓] Web interface X-Header: X-Pi-hole: The Pi-hole Web interface is working!
*** [ DIAGNOSING ]: Gravity list
-rw-r--r-- 1 root root 2641491 Feb 10 20:01 /etc/pihole/gravity.list
-----head of gravity.list------
0.0.0.0
0.r.msn.com
0.start.bz
000.0x1f4b0.com
-----tail of gravity.list------
zzz.clickbank.net
zzzezeroe.fr
zzzpooeaz-france.com
zzzrtrcm2.com
*** [ DIAGNOSING ]: contents of /etc/pihole
-rw-r--r-- 1 root root 381 Feb 10 19:40 /etc/pihole/adlists.list
https://raw.githubusercontent.com/StevenBlack/hosts/master/hosts
https://mirror1.malwaredomains.com/files/justdomains
http://sysctl.org/cameleon/hosts
https://zeustracker.abuse.ch/blocklist.php?download=domainblocklist
https://s3.amazonaws.com/lists.disconnect.me/simple_tracking.txt
https://s3.amazonaws.com/lists.disconnect.me/simple_ad.txt
https://hosts-file.net/ad_servers.txt
-rw-r--r-- 1 root root 0 Feb 5 08:52 /etc/pihole/blacklist.txt
-rw-r--r-- 1 root root 45 Feb 10 20:01 /etc/pihole/local.list
192.168.1.131 OverLoad
192.168.1.131 pi.hole
-rw-r--r-- 1 root root 234 Feb 10 20:00 /etc/pihole/logrotate
/var/log/pihole.log {
su root root
daily
copytruncate
rotate 5
compress
delaycompress
notifempty
nomail
}
/var/log/pihole-FTL.log {
su root root
weekly
copytruncate
rotate 3
compress
delaycompress
notifempty
nomail
}
-rw-r--r-- 1 root root 0 Feb 5 08:50 /etc/pihole/whitelist.txt
*** [ DIAGNOSING ]: contents of /etc/dnsmasq.d
-rw-r--r-- 1 root root 1655 Feb 10 20:01 /etc/dnsmasq.d/01-pihole.conf
addn-hosts=/etc/pihole/gravity.list
addn-hosts=/etc/pihole/black.list
addn-hosts=/etc/pihole/local.list
localise-queries
no-resolv
cache-size=10000
log-queries
log-facility=/var/log/pihole.log
local-ttl=2
log-async
dhcp-name-match=set:wpad-ignore,wpad
dhcp-ignore-names=tag:wpad-ignore
server=8.8.8.8
server=8.8.4.4
server=208.67.222.222
server=208.67.220.220
domain-needed
bogus-priv
interface=eth0
*** [ DIAGNOSING ]: contents of /etc/lighttpd
-rw-r--r-- 1 root root 3102 Feb 10 20:00 /etc/lighttpd/lighttpd.conf
server.modules = (
"mod_access",
"mod_accesslog",
"mod_auth",
"mod_expire",
"mod_compress",
"mod_redirect",
"mod_setenv",
"mod_rewrite"
)
server.document-root = "/var/www/html"
server.error-handler-404 = "pihole/index.php"
server.upload-dirs = ( "/var/cache/lighttpd/uploads" )
server.errorlog = "/var/log/lighttpd/error.log"
server.pid-file = "/var/run/lighttpd.pid"
server.username = "www-data"
server.groupname = "www-data"
server.port = 80
accesslog.filename = "/var/log/lighttpd/access.log"
accesslog.format = "%{%s}t|%V|%r|%s|%b"
index-file.names = ( "index.php", "index.html", "index.lighttpd.html" )
url.access-deny = ( "~", ".inc", ".md", ".yml", ".ini" )
static-file.exclude-extensions = ( ".php", ".pl", ".fcgi" )
compress.cache-dir = "/var/cache/lighttpd/compress/"
compress.filetype = ( "application/javascript", "text/css", "text/html", "text/plain" )
include_shell "/usr/share/lighttpd/use-ipv6.pl " + server.port
include_shell "/usr/share/lighttpd/create-mime.assign.pl"
include_shell "find /etc/lighttpd/conf-enabled -name '*.conf' -a ! -name 'letsencrypt.conf' -printf 'include \"%p\"
' 2>/dev/null"
$HTTP["url"] =~ "^/admin/" {
setenv.add-response-header = (
"X-Pi-hole" => "The Pi-hole Web interface is working!",
"X-Frame-Options" => "DENY"
)
$HTTP["url"] =~ ".ttf$" {
setenv.add-response-header = ( "Access-Control-Allow-Origin" => "*" )
}
}
$HTTP["url"] =~ "^/admin/\.(.*)" {
url.access-deny = ("")
}
include_shell "cat external.conf 2>/dev/null"
*** [ DIAGNOSING ]: contents of /etc/cron.d
-rw-r--r-- 1 root root 1704 Feb 10 20:00 /etc/cron.d/pihole
18 4 * * 7 root PATH="$PATH:/usr/local/bin/" pihole updateGravity >/var/log/pihole_updateGravity.log || cat /var/log/pihole_updateGravity.log
00 00 * * * root PATH="$PATH:/usr/local/bin/" pihole flush once quiet
@reboot root /usr/sbin/logrotate /etc/pihole/logrotate
*/10 * * * * root PATH="$PATH:/usr/local/bin/" pihole updatechecker local
50 14 * * * root PATH="$PATH:/usr/local/bin/" pihole updatechecker remote
@reboot root PATH="$PATH:/usr/local/bin/" pihole updatechecker remote reboot
*** [ DIAGNOSING ]: contents of /var/log/lighttpd
-rw-r--r-- 1 www-data www-data 1114 Feb 10 20:01 /var/log/lighttpd/error.log
2019-02-10 06:25:40: (server.c.1534) logfiles cycled UID = 0 PID = 15084
2019-02-10 14:36:08: (server.c.1828) server stopped by UID = 0 PID = 1
2019-02-10 14:36:23: (log.c.217) server started
2019-02-10 14:36:23: (server.c.1295) WARNING: unknown config-key: alias.url (ignored)
2019-02-10 19:37:55: (server.c.1828) server stopped by UID = 0 PID = 1
2019-02-10 19:37:56: (log.c.217) server started
2019-02-10 19:37:56: (server.c.1295) WARNING: unknown config-key: alias.url (ignored)
2019-02-10 19:41:57: (server.c.1828) server stopped by UID = 0 PID = 1
2019-02-10 19:41:57: (log.c.217) server started
2019-02-10 19:41:57: (server.c.1295) WARNING: unknown config-key: alias.url (ignored)
2019-02-10 19:42:31: (server.c.1828) server stopped by UID = 0 PID = 1
2019-02-10 19:42:44: (log.c.217) server started
2019-02-10 19:42:44: (server.c.1295) WARNING: unknown config-key: alias.url (ignored)
2019-02-10 20:01:19: (server.c.1828) server stopped by UID = 0 PID = 1
2019-02-10 20:01:19: (log.c.217) server started
2019-02-10 20:01:19: (server.c.1295) WARNING: unknown config-key: alias.url (ignored)
*** [ DIAGNOSING ]: contents of /var/log
-rw-r--r-- 1 pihole pihole 33021 Feb 10 20:12 /var/log/pihole-FTL.log
-----head of pihole-FTL.log------
[2019-02-10 00:02:45.913] Resizing "/FTL-strings" from 49152 to 53248
[2019-02-10 03:47:09.667] Skipping empty regex filter on line 1
[2019-02-10 03:47:09.668] Compiled 0 Regex filters and 0 whitelisted domains in 0.4 msec (0 errors)
[2019-02-10 03:47:10.002] /etc/pihole/black.list: parsed 0 domains (took 0.2 ms)
[2019-02-10 03:47:11.229] /etc/pihole/gravity.list: parsed 112857 domains (took 1226.3 ms)
[2019-02-10 09:22:36.374] Resizing "/FTL-queries" from 1605632 to 1835008
[2019-02-10 10:45:50.780] Resizing "/FTL-queries" from 1835008 to 2064384
[2019-02-10 13:36:52.441] Resizing "/FTL-queries" from 2064384 to 2293760
[2019-02-10 13:53:52.708] Resizing "/FTL-strings" from 53248 to 57344
[2019-02-10 14:36:08.303] Shutting down...
[2019-02-10 14:36:11.258] Finished final database update
[2019-02-10 14:36:11.263] ########## FTL terminated after 254850816.0 ms! ##########
[2019-02-10 14:36:26.393] Using log file /var/log/pihole-FTL.log
[2019-02-10 14:36:26.405] ########## FTL started! ##########
[2019-02-10 14:36:26.405] FTL branch: master
[2019-02-10 14:36:26.405] FTL version: v4.2.1
[2019-02-10 14:36:26.406] FTL commit: 5f98312
[2019-02-10 14:36:26.406] FTL date: 2019-02-06 18:36:55 -0800
[2019-02-10 14:36:26.406] FTL user: pihole
[2019-02-10 14:36:26.406] Starting config file parsing (/etc/pihole/pihole-FTL.conf)
[2019-02-10 14:36:26.407] SOCKET_LISTENING: only local
[2019-02-10 14:36:26.407] AAAA_QUERY_ANALYSIS: Show AAAA queries
[2019-02-10 14:36:26.407] MAXDBDAYS: max age for stored queries is 365 days
[2019-02-10 14:36:26.407] RESOLVE_IPV6: Resolve IPv6 addresses
[2019-02-10 14:36:26.407] RESOLVE_IPV4: Resolve IPv4 addresses
[2019-02-10 14:36:26.407] DBINTERVAL: saving to DB file every minute
[2019-02-10 14:36:26.407] DBFILE: Using /etc/pihole/pihole-FTL.db
[2019-02-10 14:36:26.407] MAXLOGAGE: Importing up to 24.0 hours of log data
[2019-02-10 14:36:26.408] PRIVACYLEVEL: Set to 0
[2019-02-10 14:36:26.408] IGNORE_LOCALHOST: Show queries from localhost
[2019-02-10 14:36:26.408] BLOCKINGMODE: Null IPs for blocked domains
[2019-02-10 14:36:26.408] REGEX_DEBUGMODE: Inactive
[2019-02-10 14:36:26.408] ANALYZE_ONLY_A_AND_AAAA: Disabled. Analyzing all queries
[2019-02-10 14:36:26.408] DBIMPORT: Importing history from database
[2019-02-10 14:36:26.408] PIDFILE: Using /var/run/pihole-FTL.pid
-----tail of pihole-FTL.log------
[2019-02-10 20:12:07.314] WHITELISTFILE: Using /etc/pihole/whitelist.txt
[2019-02-10 20:12:07.314] BLACKLISTFILE: Using /etc/pihole/black.list
[2019-02-10 20:12:07.314] GRAVITYFILE: Using /etc/pihole/gravity.list
[2019-02-10 20:12:07.314] REGEXLISTFILE: Using /etc/pihole/regex.list
[2019-02-10 20:12:07.314] SETUPVARSFILE: Using /etc/pihole/setupVars.conf
[2019-02-10 20:12:07.314] AUDITLISTFILE: Using /etc/pihole/auditlog.list
[2019-02-10 20:12:07.314] Finished config file parsing
[2019-02-10 20:12:07.314] Skipping empty regex filter on line 1
[2019-02-10 20:12:07.314] Compiled 0 Regex filters and 0 whitelisted domains in 0.2 msec (0 errors)
[2019-02-10 20:12:07.316] Database successfully initialized
[2019-02-10 20:12:07.317] New forward server: 8.8.4.4 (0/4096)
[2019-02-10 20:12:07.318] New forward server: 208.67.220.220 (1/4096)
[2019-02-10 20:12:07.320] New forward server: 208.67.222.222 (2/4096)
[2019-02-10 20:12:07.331] Resizing "/FTL-strings" from 4096 to 8192
[2019-02-10 20:12:07.361] Resizing "/FTL-strings" from 8192 to 12288
[2019-02-10 20:12:07.387] New forward server: 8.8.8.8 (3/4096)
[2019-02-10 20:12:07.395] Resizing "/FTL-queries" from 229376 to 458752
[2019-02-10 20:12:07.526] Resizing "/FTL-queries" from 458752 to 688128
[2019-02-10 20:12:07.673] Resizing "/FTL-queries" from 688128 to 917504
[2019-02-10 20:12:07.812] Resizing "/FTL-queries" from 917504 to 1146880
[2019-02-10 20:12:07.953] Resizing "/FTL-queries" from 1146880 to 1376256
[2019-02-10 20:12:07.986] Resizing "/FTL-strings" from 12288 to 16384
[2019-02-10 20:12:08.091] Resizing "/FTL-queries" from 1376256 to 1605632
[2019-02-10 20:12:08.226] Resizing "/FTL-queries" from 1605632 to 1835008
[2019-02-10 20:12:08.362] Resizing "/FTL-queries" from 1835008 to 2064384
[2019-02-10 20:12:08.462] Imported 35676 queries from the long-term database
[2019-02-10 20:12:08.464] -> Total DNS queries: 35676
[2019-02-10 20:12:08.464] -> Cached DNS queries: 600
[2019-02-10 20:12:08.464] -> Forwarded DNS queries: 31606
[2019-02-10 20:12:08.464] -> Exactly blocked DNS queries: 3462
[2019-02-10 20:12:08.465] -> Unknown DNS queries: 8
[2019-02-10 20:12:08.465] -> Unique domains: 650
[2019-02-10 20:12:08.465] -> Unique clients: 7
[2019-02-10 20:12:08.465] -> Known forward destinations: 4
[2019-02-10 20:12:08.465] Successfully accessed setupVars.conf
*** [ DIAGNOSING ]: contents of /dev/shm
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-0
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-1
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-2
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-3
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-4
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-5
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-client-6
-rw------- 1 pihole pihole 163840 Feb 10 20:12 /dev/shm/FTL-clients
-rw------- 1 pihole pihole 112 Feb 10 20:12 /dev/shm/FTL-counters
-rw------- 1 pihole pihole 131072 Feb 10 20:12 /dev/shm/FTL-domains
-rw------- 1 pihole pihole 163840 Feb 10 20:12 /dev/shm/FTL-forwarded
-rw------- 1 pihole pihole 28 Feb 10 20:12 /dev/shm/FTL-lock
-rw------- 1 pihole pihole 212992 Feb 10 20:12 /dev/shm/FTL-overTime
-rw------- 1 pihole pihole 2064384 Feb 10 20:12 /dev/shm/FTL-queries
-rw------- 1 pihole pihole 16384 Feb 10 20:12 /dev/shm/FTL-strings
*** [ DIAGNOSING ]: Locale
LANG=
*** [ DIAGNOSING ]: Pi-hole log
-rw-r--r-- 1 pihole pihole 16712833 Feb 10 20:12 /var/log/pihole.log
-----head of pihole.log------
Feb 10 00:00:02 dnsmasq[21343]: query[A] connector.myqnapcloud.com from 192.168.1.2
Feb 10 00:00:02 dnsmasq[21343]: cached connector.myqnapcloud.com is <CNAME>
Feb 10 00:00:02 dnsmasq[21343]: forwarded connector.myqnapcloud.com to 208.67.222.222
Feb 10 00:00:02 dnsmasq[21343]: query[A] connector.myqnapcloud.com from 192.168.1.2
Feb 10 00:00:02 dnsmasq[21343]: forwarded connector.myqnapcloud.com to 208.67.222.222
Feb 10 00:00:02 dnsmasq[21343]: query[A] connector.myqnapcloud.com from 192.168.1.3
Feb 10 00:00:02 dnsmasq[21343]: forwarded connector.myqnapcloud.com to 208.67.222.222
Feb 10 00:00:02 dnsmasq[21343]: reply connector.myqnapcloud.com is <CNAME>
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.5.24.234
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.203.157.121
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.202.129.223
Feb 10 00:00:02 dnsmasq[21343]: reply connector.myqnapcloud.com is <CNAME>
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.203.157.121
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.202.129.223
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.5.24.234
Feb 10 00:00:02 dnsmasq[21343]: reply connector.myqnapcloud.com is <CNAME>
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.203.157.121
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.202.129.223
Feb 10 00:00:02 dnsmasq[21343]: reply qcloud-pr-connector-16242653.us-east-1.elb.amazonaws.com is 52.5.24.234
Feb 10 00:00:03 dnsmasq[21343]: query[A] www.googletagmanager.com from 192.168.1.119
********************************************
********************************************
[✓] ** FINISHED DEBUGGING! **
* The debug log can be uploaded to tricorder.pi-hole.net for sharing with developers only.
* For more information, see: https://pi-hole.net/2016/11/07/crack-our-medical-tricorder-win-a-raspberry-pi-3/
* If available, we'll use openssl to upload the log, otherwise it will fall back to netcat.
[i] Debug script running in automated mode
* Using openssl for transmission.
***********************************
***********************************
[✓] Your debug token is: c5d38sqcfb
***********************************
***********************************
* Provide the token above to the Pi-hole team for assistance at
* https://discourse.pi-hole.net
* Your log will self-destruct on our server after 48 hours.
* A local copy of the debug log can be found at: /var/log/pihole_debug-sanitized.log