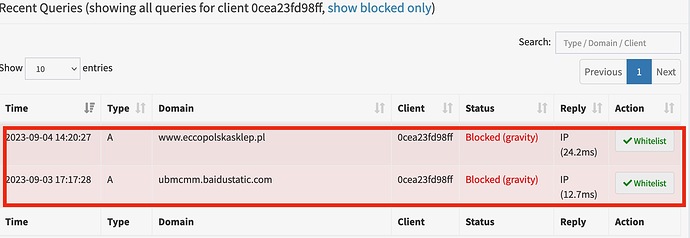
I just saw this in my clients part of the pihole section list and have no idea what this means? I’m concerned because it attempts to call to two sites that are deemed malicious see attached photos. It has blocked the sites, but still have no idea what @if12. It strikes me as very weird.
Any assistance would be incredible and put my mind at ease. I can’t seem to get any information based on searching.
Thank you in advance, community.
Can you create a debug log please and post the token URL here? The command is
pihole -d
or use Tools > Generate debug log > Upload debug log and provide Debug Token
It looks like you might have some container software running on your Pi, and perhaps something running in one of those is trying to reach these domains. The debug log won't reveal anything about that, but will at least show how the Pi's networking is set up and what other services may be running, which can give some clues.
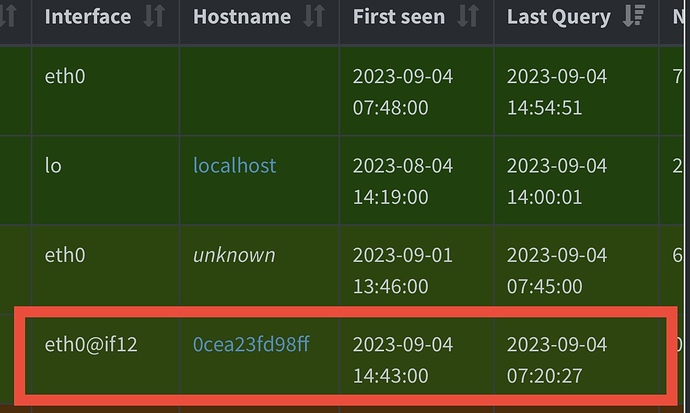
Thankyou. You are running Docker, and running the Pi-hole Docker image in one of the containers. The debug log shows that the Pi-hole container's network interface is named eth0@if18.
I've not used Docker so I'm making some assumptions here – someone with experience may be able to advise better.
It looks to me like another container, which has a network interface named eth0@if12, is using Pi-hole for its DNS. The Pi-hole Docker image is able to see the container interface names. That container is requesting those two domains you flagged as malicious.
Are you able to identify the container in question and establish what it is being used for? There may be some application on there which is trying to send telemetry to those domains. I'd be inclined to keep it blocked unless you uncover a reason not to.
VirusTotal flags the first domain as malicious and the second domain as clear. But bear in mind:
- These tests are testing the web service running on these domains. That may be unrelated to any application specific protocols running on these domains. For example it could be that the web service hosts a content management system which was outdated and some fake spam sites have been uploaded to it, causing it to now be flagged.
- VirusTotal (and other scanners) will often flag things as "malicious" when they exhibit behaviour which can be used to support something else that really is malicious. For example I had a window manager utility which was always flagged as "virus" by these tools just because it can be used to hide windows from appearing, which is something that a virus might want to do.
Thank you for the insight. Is there anyway to find out what device on my network is calling out to that address or any other address that might be malicious? I’m now getting this as well:
eth0@if18 calling to another potential malicious site, and it’s being blocked. Is it absolutely a container, or could it be a file residing on my computer/host Mac mini running the pihole, as well as a media server?
Inside the Pi-hole container, on the command line, what is the output of ip -br addr? Also, which network mode are you using? Host, bridge, macvlan?
I had to leave the house, and will get your questions answered when I get back. Do you want a screen shot of the listed devices. Also I use bridge, as the standard default afaik.
No... Just copy and paste the command output in text.
You can format the text block, selecting the text and pressing the  button, or using CTRL+E.
button, or using CTRL+E.