(Could you consider to post console output as text?
It would be easier to read, easier to copy and paste from, easier to redact for sensitive information, and it uses less storage. I'll help with the formatting if required.)
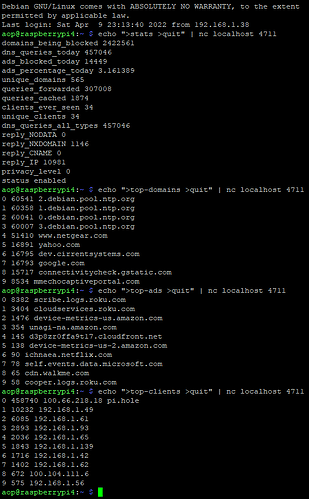
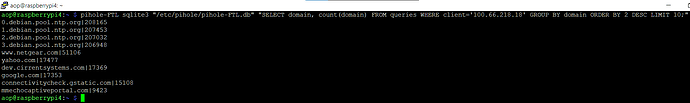
DNS traffic from your Tailscale IP 100.66.218.18 seems desperate to get the IP of a time server. Correct time information is crucial for many cryptographic procedures, so may be as well for your Tailscale VPN service.
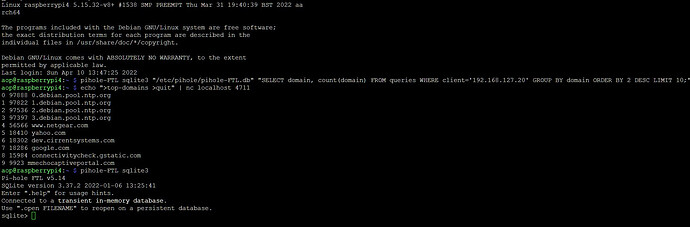
Your debug log shows a process tailscaled running, which I assume is your Tailscale VPN software.
Note that DNS resolution on Pi-hole's host system is completely independent from Pi-hole's DNS operation:
While Pi-hole is accepting incoming DNS requests from your clients and forwarding allowed requests to its configured upstream DNS servers, its host system will continue to use whatever it is configured for.
Your debug log shows your host system to point to 1.1.1.1 for DNS resolution:
*** [ DIAGNOSING ]: contents of /etc
-rw-r--r-- 1 root root 45 Apr 11 11:45 /etc/resolv.conf
nameserver 1.1.1.1
Thus, it is not yet clear why your tailscaled service would use Pi-hole for DNS at all.
Moreover, it is strange that dig 0.debian.pool.ntp.org failed because no servers could be reached, while a dig directed at @1.1.1.1 would resolve correctly, when both of those digs should have been handled by 1.1.1.1.
Please run the following commands on your RPi:
dig flurry.com
dig flurry.com @192.168.1.186
dig flurry.com -p 5335 @127.0.0.1
I'd expect to see IP address replies for all of those but the one that goes to your Pi-hole's IP.
As an attempt to address your issue for the moment, you could try to stop your Tailscale VPN service on your Pi-hole host (if you are currently not travelling), probably by running:
sudo systemctl stop tailscaled.service
But please:
Run the three dig commands twice - once before you stop Tailscale, and once after.