DL6ER
May 22, 2025, 1:07pm
10
It took quite some time but here is the proposed automatic renewal of the self-generated certificates in case of certificated with short-term validity:
development ← new/renew_tls_cert
opened 12:46PM - 22 May 25 UTC
# What does this implement/fix?
Implement automatic TLS/SSL certificate renew… als. The validity can now be configured through `webserver.tls.validity` defaulting to `47 days`. Context is that there are recommendation coming into effect over the next few year which are reducing the allowed/acceptable validity in steps down to as short as 47 days.
See the linked Discourse discussion for further context.
---
**Related issue or feature (if applicable):** https://discourse.pi-hole.net/t/apple-clients-do-not-trust-tls-certificates-with-long-validity-periods/79235
**Pull request in [docs](https://github.com/pi-hole/docs) with documentation (if applicable):** N/A
---
**By submitting this pull request, I confirm the following:**
1. I have read and understood the [contributors guide](https://docs.pi-hole.net/guides/github/contributing/), as well as this entire template. I understand which branch to base my commits and Pull Requests against.
2. I have commented my proposed changes within the code.
3. I am willing to help maintain this change if there are issues with it later.
4. It is compatible with the [EUPL 1.2 license](https://opensource.org/licenses/EUPL-1.1)
5. I have squashed any insignificant commits. ([`git rebase`](http://gitready.com/advanced/2009/02/10/squashing-commits-with-rebase.html))
## Checklist:
- [x] The code change is tested and works locally.
- [x] I based my code and PRs against the repositories `developmental` branch.
- [x] I [signed off](https://docs.pi-hole.net/guides/github/how-to-signoff/) all commits. Pi-hole enforces the [DCO](https://docs.pi-hole.net/guides/github/dco/) for all contributions
- [x] I [signed](https://docs.github.com/en/authentication/managing-commit-signature-verification/signing-commits) all my commits. Pi-hole requires signatures to verify authorship
- [x] I have read the above and my PR is ready for review.
The proposed validity range is reduced from 30 to 2 years in here, but this is not set in stone. I'd like to foster a discussion here for what you think is needed.
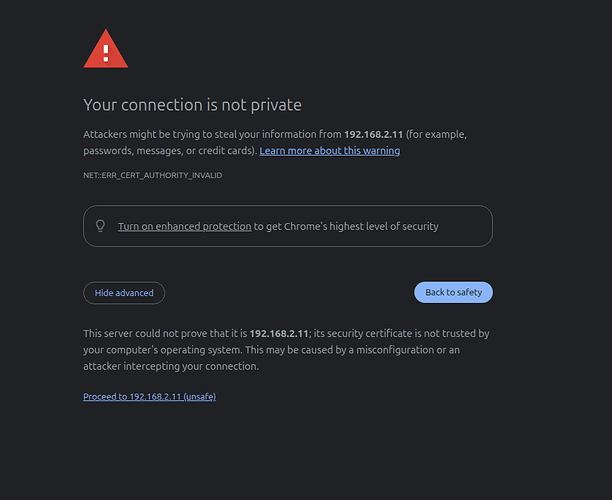
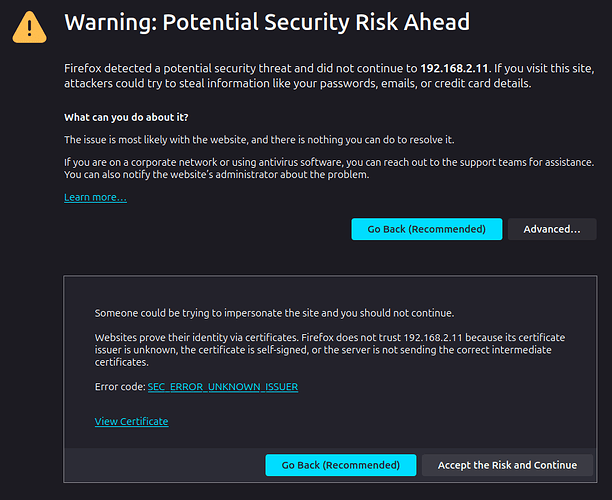
Note: Short lifetimes may cause some inconvenience to users. Whenever the certificate is automatically regenerated, users will again have to confirm that they want the browser to trust the new certificate:
(Chromium)
(Firefox)